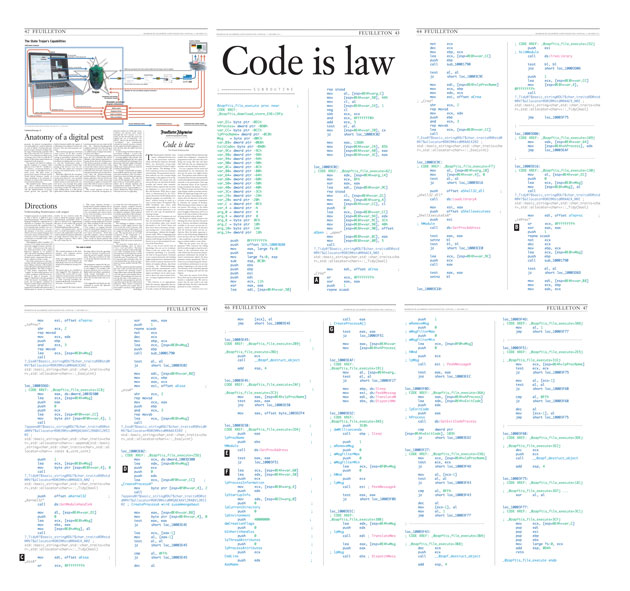
Code Is Law
Code Is Law
The Staatstrojaner (literally "state trojan", colloquial German term for the government malware) whose self-destruct function obviously failed, was discovered, reverse-engineered and analyzed by Chaos Computer Club hackers. The findings, if the CCC's analysis is correct, are conclusive and alarming: The government surveillance software not only contains illegal functionality, it also appears to be so significantly flawed, that anyone who can encrypt the key can also hack all similar versions and control them remotely. Should evidence captured this way have any legitimacy in a court of law? And, first and foremost: What does it mean when, as demonstrated by the CCC, anyone that knows the IP address of the infected computer can install fake "evidence" without leaving so much as a trace or little chance of acquittal?...
But there's more: Computers are not only instruments of communication, they are instruments of thought. A series of screenshots taken every second (forwarded to the United States and from there back to Germany) of someone creating a text – never emails or digital monologues – shadows the thought process itself. What is happening here makes your hair stand on end.
Introduction
by John Brockman
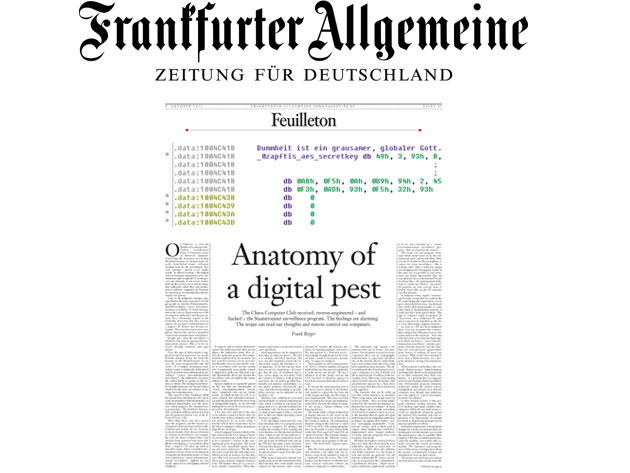
Every few years Frank Schirrmacher, co-publisher and Feuilleton editor of the German national newspaper Frankfurter Allgemeine Zeitung, startles Germany with an audacious piece of publishing. Last month, he devoted the entire of the Sunday Feuilleton to an expose that included page after page of malware software code reverse-engineered by computer hackers from "the Staatstrojaner surveillance program" code that the German government has been illegally inserting into users' computer system. "The findings are alarming," notes FAZ. "The trojan can read our thoughts and remote control our computers."
Such trojan-horse key-logging software, known as a RAT (remote administration tool) is hardly new. The FBI, supposedly with legal search warrants, has been doing this since at least 2000. In 2009, John Markoff broke the story in The New York Times about "Ghostnet", a vast electronic spying operation that infiltrated computers and stole documents from hundreds of government and private offices in 103 countries. The system was controlled from computers based almost exclusively on a Chinese offshore island, although there was no conclusive evidence that the Chinese government was involved. Adding to the still unsolved mystery is the fact that the only major country not a victim of the infiltration was the United States.
What is unique in the case of German State Trojan horse is that the center-right national newspaper, with the aid of the German hacker community, has caught the government red-handed in the illegal activity of spying on, and as some might say, controlling their own citizens.
So here we are, a month away from celebrating the centenary of Alan Turing, the man who is identified with the idea of computation itself, and what do we have?
"I think it is an amazing piece that opens entire 55-gallon drums of worms," says George Dyson, author of the forthcoming Turing's Cathedral, a history of the birth of the digital age. "It reminds me of the scene in The Lives of Others where you get to see inside the Stazi's secret bunker that held the thousands of glass jars with the captured scent of all suspicious people—and you know this is just the tip of the iceberg. Can you imagine what's going on in China, or the USA? Not just "reading our thoughts" but, as we do more and more of our thinking with our devices, getting closer and closer to writing our thoughts as well. Do we want to continue to live in a world where we're completely comfortable with cameras everywhere, all the time, and all our e-mail is retrievable forever? It's becoming the new normal now and Schirrmacher's piece is a wake up call."
While most of the Turing Centenary celebrations already in the works will no doubt paint a rosy picture of the impact of the computational idea, Schirrmacher reminds us of a much darker side to what Turing has wrought. There's more to consider—much more—than Steve Jobs's personality, Facebook privacy settings, Arab springs, Google search algorithms, Amazon ebook pricing, Twitter revolutions, smartphone patent wars.
Click here to download the English-language pdf of the FAZ Feuilleton edition.
Comments?
Conversation: John Markoff, Douglas Rushkoff, Clay Shirky, Nicholas Carr, Evgeny Morozov